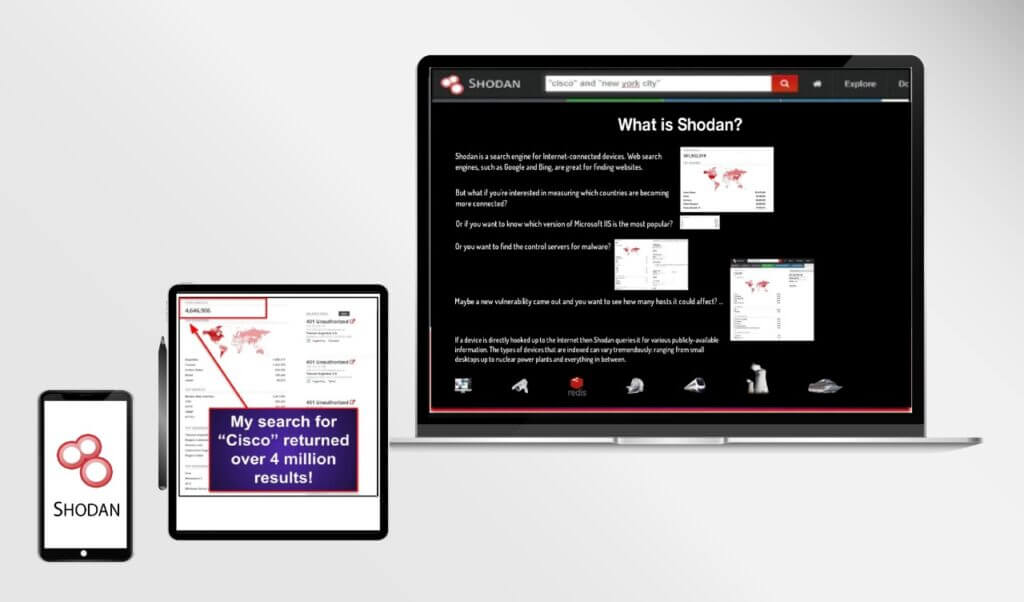
Shodan is a search engine that is designed to search for Internet-connected devices. This includes everything from servers to routers to smart devices (Internet of Things devices) such as baby monitors and smart TVs.
Because of its detection capabilities, Shodan is a powerful tool used by cybersecurity researchers and experts to seal up gaps in their networks. It is also used by hackers to exploit security vulnerabilities.
Read on to learn how you can use Shodan to protect the devices on your network from hackers.
What is Shodan?
Shodan was created in 2009 by John Matherly and is named after SHODAN, a character from the video game series System Shock.
It works by requesting connections to IP addresses on the Internet and then indexing the information for future reference. This is similar to how other search engines work, such as Google.
An IP address is a unique identifier that every device connected to the Internet has. IP addresses allows Internet-capable devices to connect with one another and also allow individual devices to be identified. VPNs can be used to hide your IP address when accessing the Internet.
When a device is connected to the Internet, it does so via a “port,” a connection that is designed to transfer a specific type of data. Different types of data, such as email, printers, routers, and browsers all have different ports.
If a device’s port is open, it can be accessed, which allows devices to connect with one another. The connection process is sometimes called “knocking.” When a device “knocks” at an open port, the other device sends a “banner,” a data packet that completes the connection.
When Shodan indexes IP addresses, it “knocks” at every port of every known IP address continuously. Many ports will then transmit banners that provide Shodan with metadata that can then be indexed. Metadata indexed by Shodan can include device names, IP addresses, port numbers, organization names, device locations, and even default logins and passwords of some devices.
How Shodan Work?
If your device is connected to the Internet, there is a chance it can appear in Shodan’s search engine. This not only includes computers or smartphones, but routers, security cameras, smart TVs, and even traffic light systems and prison pay phones.
Note that just because Shodan indexes public information about devices, that doesn’t mean those devices are publicly accessible. Traffic light systems and prison pay phones may appear on a Shodan search, but these systems are typically protected by tight security that doesn’t appear publicly.
However, Shodan is valuable because it shows how much computer security information can be found freely on the Internet. If you have smart devices that are connected to the Internet and you haven’t changed the default password, for example, hackers can easily use Shodan to find the devices and access them.
How to Use Shodan Search Engine
Shodan is accessible to the public, but unlike Google, it’s not as user-friendly. Here are some tips on how you can use Shodan to secure your devices against hackers.
While you can enter a search string into Shodan much as you would any other search engine, doing so will make it difficult to find the devices you are looking for, since you will likely need to sort through millions of results. To narrow your search down, you’ll need to use Shodan’s search filter system.
Shodan allows you to filter your searches in a number of different ways, including by city, country, GPS coordinates, hostname, software or product name, operating system, port, and more. By using these search filters, you’ll be able to refine your results and locate your devices in Shodan’s results.
Note that in order to use Shodan’s search filters, you’ll need to sign up for an account. Shodan offers several account tiers, including a free account service with limited features. You can purchase membership tiers that offer additional features, such as network monitoring for thousands of IP addresses.
Best Ways to Remove Shodan
You may be wondering if it’s possible to remove your devices—especially your Internet of Things (IoT) devices—from Shodan’s search results.
Unfortunately, it’s not possible to completely remove your devices from Shodan without disconnecting them from the Internet entirely. However, you can take steps to limit the amount of information that Shodan can collect about your devices.
The first thing you can do is change your login and password details. Don’t use the default logins and passwords that come with your smart devices, because those will be automatically indexed by Shodan. Use unique, hard-to-guess passwords so your devices remain protected.
You should also minimize the amount of banner information your devices provide. Banner metadata can give away your device’s location and more. Fortunately, many devices also allow you to customize banner information, limiting it from being exposed to the wider world.
Finally, if you haven’t already, install a network firewall to prevent unauthorized requests to any devices connected to your router.
Is Shodan Legal?
Given that Shodan is sometimes used by hackers, you may be wondering if the site is legal.
The answer is yes. Shodan doesn’t search out information that is secret; it merely collects information that is already freely accessible on the Internet and catalogues it for future reference, in the same way that other search engines do.
In fact, Shodan is used by cybersecurity professionals and businesses to plug holes in their networks, which makes it an invaluable tool in the fight against hackers and cybercriminals.
Shodan: The Bottom Line
Shodan is an extremely powerful tool when it comes to online security. Its ability to detect and catalog online devices may seem intimidating, but this information is extremely valuable as it allows individuals to see if their devices are vulnerable and correct these issues.
By following the tips in this guide, you’ll be able to use Shodan to secure your devices against hackers and keep yourself safe online.